Metadata Petting Zoo
Cellphones make available large amounts of personal information about you in public airspace. I propose building a metadata petting zoo to raise awareness for this issue and some possible solutions.
This broadcasting of metadata is a necessity for you using your phone. It cannot be disabled until cellphone technology is recreated from the ground up with privacy in mind. It doesn’t require hidden surveillance technology but makes use of the most common network systems such as Wifi, LTE, GSM and Bluetooth.
This post will explain the threat from metadata and show you how I want to make it visible. A follow-up will explain how we can deal with this information without becoming fearful or ignorant.
So lets think a bit about phone metadata. In order to be able to connect to networks as they become available your phone actively searches for access points. For example, when you enter your home your phone connects to your Wifi automatically. This is because it »asks around« on the airspace if your Wifi is around, until it finally gets an answer when you get home. But it doesn’t just ask around then but all the time, while you are in shops, while you are walking past advertisements, while you are on trains. These requests make it possible to detect the proximity of your phone for anyone who uses special scanning devices to listen in on these requests. As most people carry their phones on their body all of the time, proximity of their phone directly translates into proximity of them as a person.
This doesn’t just work for Wifi, but also for Bluetooth and even the phone networks that are used for calls and text messages. Anybody who places scanning devices in public spaces can therefore create detailed movement profiles of people.
The possibilites are even greater if this approach is combined with other methods of data collection.
Example: The Shopper

So you leave your house to make some errands. On the bus stop there is an advertisement for a soft drink. A tiny scanner hidden behind the ad detects the presence of your phone while you are waiting for the bus and records that the owner of that phone saw the ad.
Some time later you are in a supermarket, paying for your groceries. Among them is a bottle of just that softdrink. The cashier scans your items while you wait – at the same time a scanner within the cash register detects your phone. Now the supermarket can sell the list of items you bought, which has been connected to the IDs of your phone and your credit card data.
A hedge fund buys this information from both the supermarket and the company placing the advertisement sign. They now know that you looked at the ad and bought the soft drink 39 minutes later. They adjust their investment to maximize profit.
Combine and Conquer
And this is not the first time they combined this information. The last time you were at the supermarket you were carrying the same cell phone with you. So all of your past purchases can be connected to your movement profile. You were carrying that same phone everywhere! Who knows where scanners were registering your presence? They are cheap, easy to hide and impossible to detect from the outside.
The card that you used to pay at the supermarket is connected to your name. After scanning your phone a couple of times while you are paying with your card, a connection can be established between the anonymous ID that is transmitted by your phone and the identity data at your bank.
The combination of profiles established through different means of collection personal data doesn’t just add dimensions, it also allows to fill in gaps in the data. If you were paying some purchase with cash to stay anonymous but still carrying the phone you used while you were paying with a card another time, these pieces of data can be connected and your anonymous cash transaction is not anonymous anymore.
The collection and combination of such data profiles allows for the creation of models of human behavior of incredible fidelity. They make populations predictable and therefore controllable. They create immense power and contain it in the hands of those who have the means to amass and process these data collections.
This mechanism can only be avoided by recreating cellular technology with privacy as a top priority. This will only happen if there is demand for it, which requires knowledge and awareness in the first place.
A Metadata Surveillance Petting Zoo
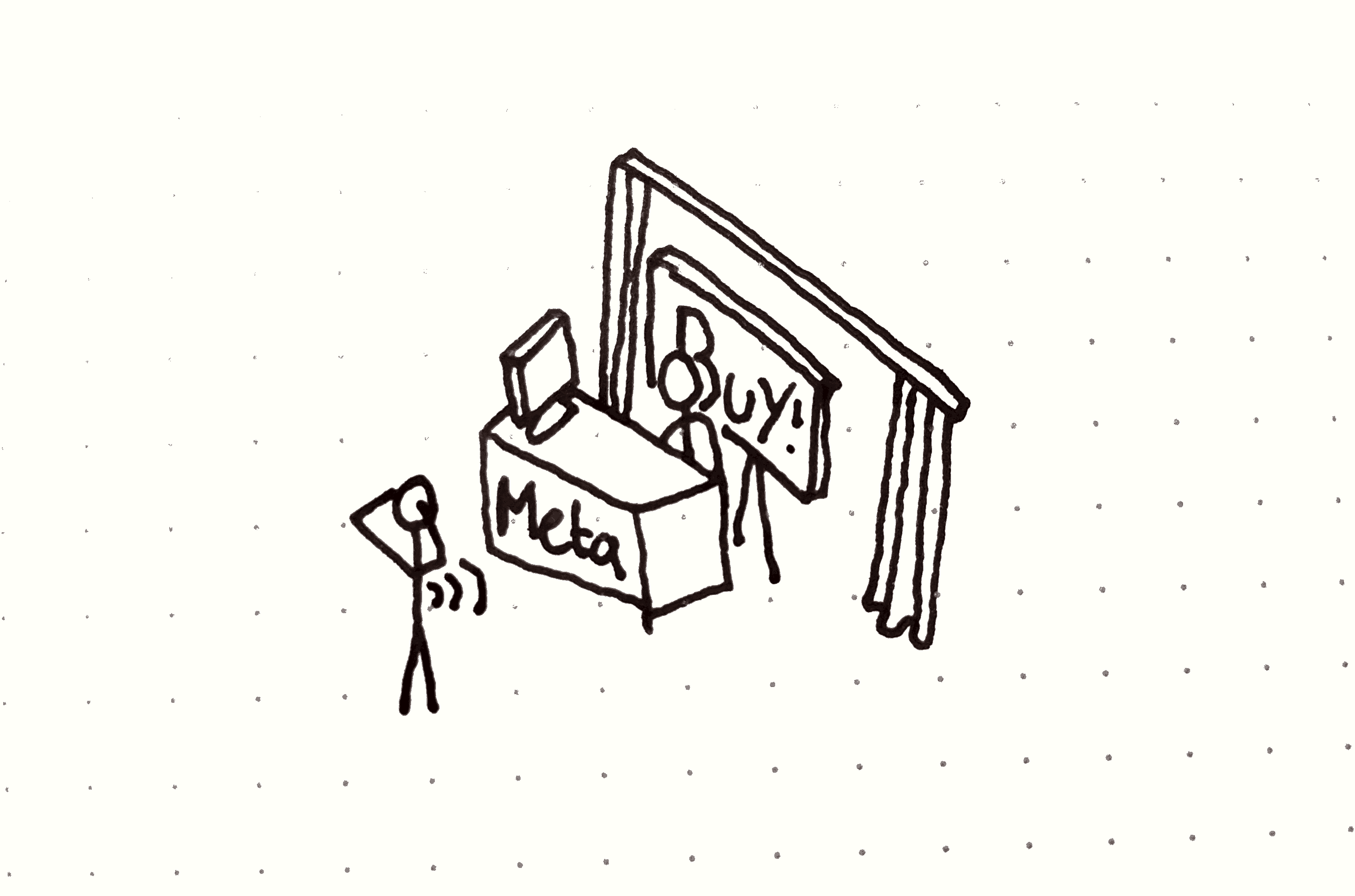
To make this surveillance technique visible I propose a metadata surveillance petting zoo. The setup consists of two parts, which are encountered sequentially by the interested visitor:
The first part recreates the bus stop from the above story. A printed advertising, similar to those placed in many public places, uses friendly lettering and bright colors to promote Metadata: »Enabling everyone from the BND and NSA to your friendly hedge fund to collect intel about the population, control their desires and lead them to decisions«. A spooky camera, installed on top of the ad, places the object in the context of traditional surveillance imagery. A sticker with common iconography warns of video surveillance.
However, the camera is actually recording a video of the visitor who is reading the ad. At the same time a scanning device within the ad records their phone’s identifying metadata (WIFI SSID list, Wifi Mac address, Bluetooth device id).
The second part is placed physically separated from the first part, but in a way so that it is encountered after that by visitors. It recreates a cash register. The visitor takes on the role of a politican, hedge fund manager, or similar person with interest in gaining power. If they want, they can make a buy order for personal information by pushing a button. While they are informed about this, a second scanner hidden in the cash register re-identifies their device.
When pushing the button, a computer screen is revealed that shows the previously recorded video of the person and announces: »Buyer has been reidentified. The marketing campaign was successfull, metadata has been sold and profit was made.«
The visitor becomes aware that their phone allows tracking them across physical space even without any action on their part.
And now, you
So what do you think? Please send me your thoughts and criticism on Twitter or via email.
I am also looking for:
- people with knowledge of passive GSM/WIFI/Bluetooth scanners
- people who have (or can build) an ad display or cash register
- people who would like to help with this in other ways
to make this happen.
To be continued: part 2 of this post
All of this information presents a scenario where we are helplessly exposed to exploitation by powerful actors. This can only result in either fear or ignorance, unless there is a path for action or reinterpretation. Nobody wants that! Part 2 of this post will discuss specific paths of action that we can take in order to reduce the impact of these technologies. Also there are open problems without a good solution that we will have to think about. These include making filter bubbles transparent and controllable as well as shielding news media from marketing campaigns. Stay tuned!